Attach a Cluster with Networking Restrictions

When do I Need to use a Secure Tunnel?
When attaching a cluster to DKP, the Management cluster initiates an outbound connection to the cluster you wish to attach. This is not possible if the cluster you want to attach (Managed or Attached) has networking restrictions and is not exposed, for example, because it is in a private network, or its API is not accessible from the same network as the Management cluster. This is what we call a network-restricted cluster.
-1-1.png?inst-v=d47a54c4-ff5d-4ef9-b867-41e26a099d62)
Diagram: Attachment not possible when cluster is in a private network.
Use a tunnel when you want to attach a cluster that is in a DMZ, behind a NAT gateway, behind a proxy server, firewall, or requires additional access information.
How Does the Tunneled Attachment work?
DKP can create a secure tunnel to enable the attachment of clusters that are not directly reachable.
To create a secure tunnel, you must provide a configuration for the tunnel in the cluster you want to attach. After you apply that configuration, the cluster you want to attach will establish a secure tunnel with the Management cluster, and make an attachment request.
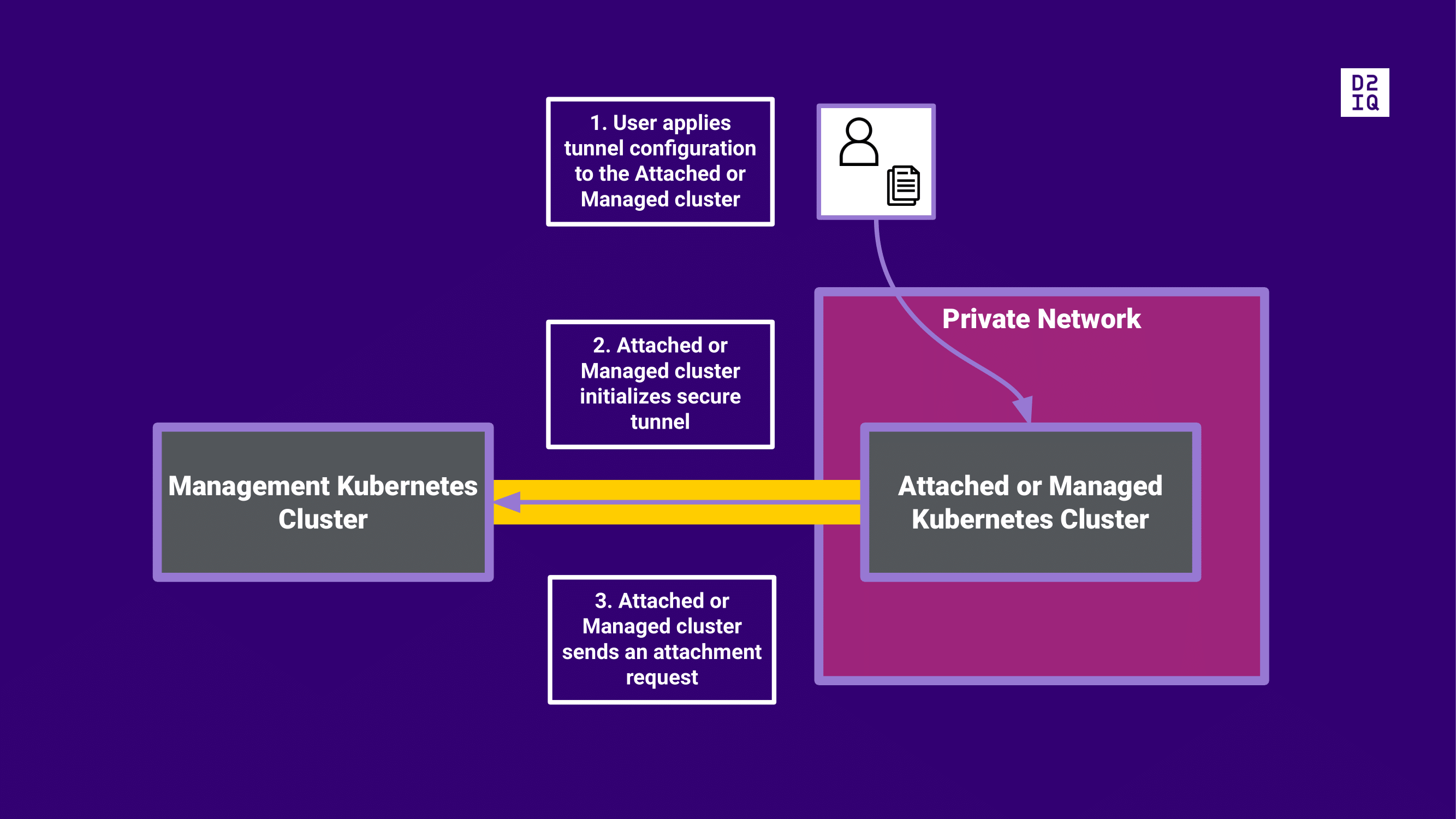
Diagram: Attachment through a secure tunnel
After the attachment request is accepted and the connection between clusters is established, both clusters will allow bilateral communication.
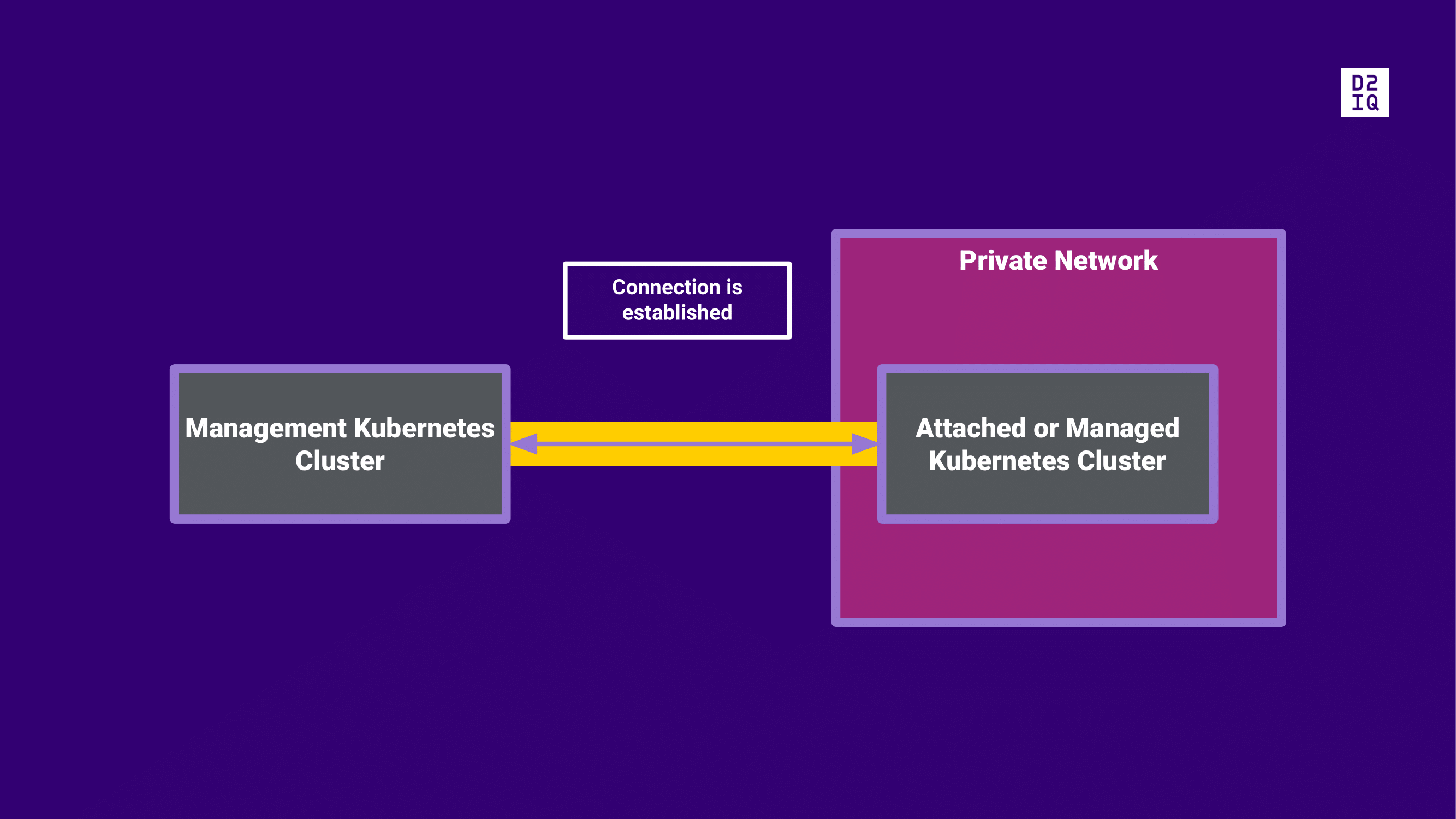
Diagram: Connection between clusters is established
What are the Steps to Attach a Cluster via a Tunnel?
Ensure you meet the prerequisites for a tunneled attachment, and then attach the cluster with the UI or CLI:
.png)